eWPTX (Web Application Penetration Tester eXtreme) v3 Certification Experience
Introduction
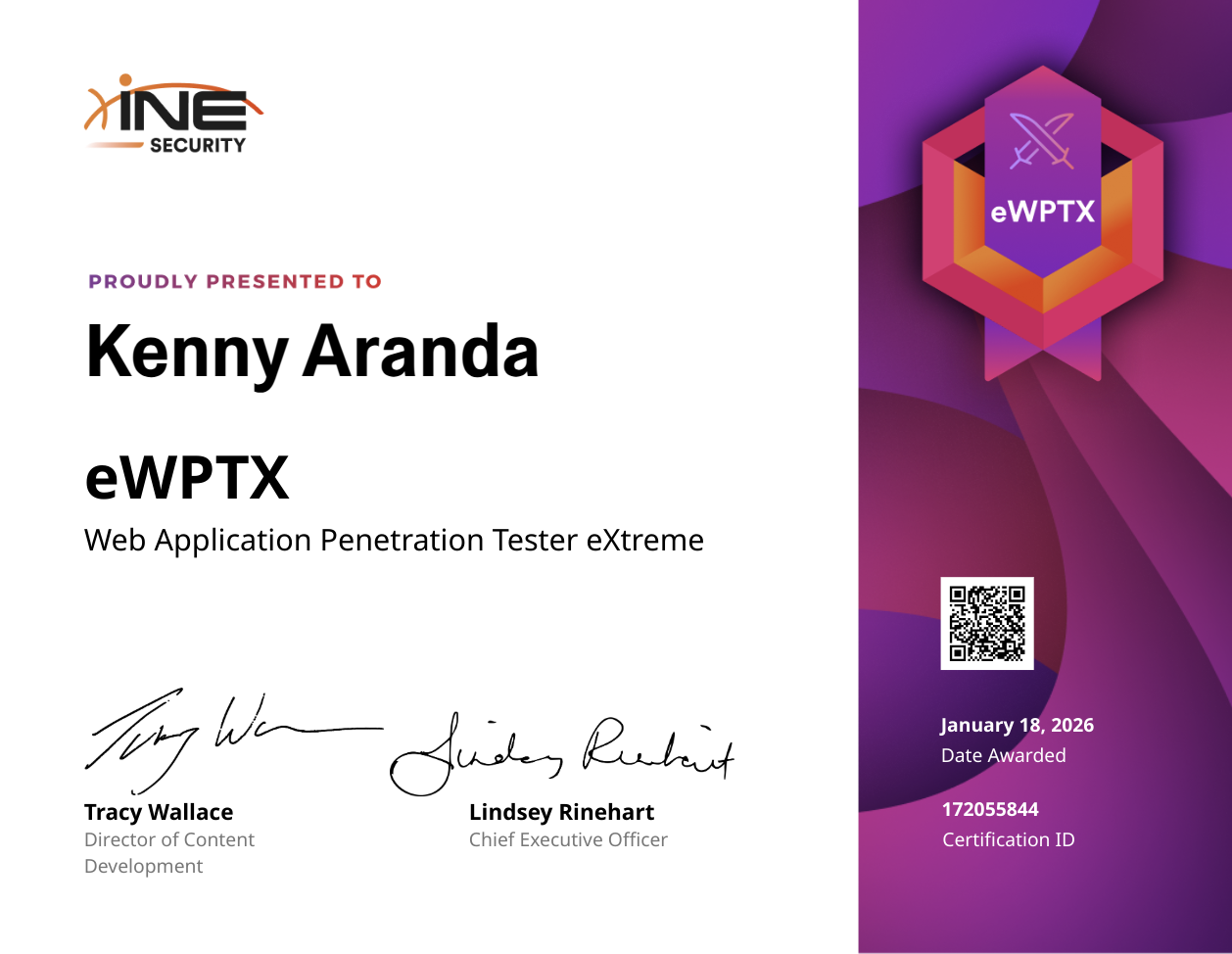
In this post, I want to share my journey preparing for and successfully achieving the eLearnSecurity Web application Penetration Tester eXtreme (eWPTX) certification. Unlike entry-level certifications, this exam pushes you to the limit regarding advanced web exploitation, filter evasion, and complex attack chaining.
Why I Chose eWPTX
- Advanced Scope: It moves beyond the “basics” of the OWASP Top 10 into complex scenarios like serialization attacks and advanced SQL injection.
- Real-World Scenarios: The focus is on bypassing security controls (WAFs, input sanitization), which mirrors the hardened environments I encounter in actual client engagements.
- Manual Exploitation: It enforces a deep understanding of the underlying technology, requiring you to construct payloads manually rather than relying on automated scanners.
Preparation Strategy
Given the “eXtreme” nature of this exam, I had to refine my study methodology:
- INE/eLearnSecurity Courseware: I focused heavily on the modules regarding XML External Entity (XXE), Java Deserialization, and Server-Side Template Injection (SSTI).
- PortSwigger Web Security Academy: I supplemented the official course by grinding through Practitioner and Expert level labs on PortSwigger to sharpen my Burp Suite skills.
- Custom Payload Lists: I spent time building my own lists for fuzzing, specifically targeting different encoding methods to bypass filters.
- Code Review: I refreshed my PHP and Java knowledge to better predict backend behavior when operating blind.
Exam Experience
The exam is a rigorous practical assessment..
- Filter Evasion is Key: The vulnerabilities are there, but they are often behind strict filtering logic. If you rely solely on tools like SQLMap, you will likely fail.
- Rabbit Holes: There are several paths that look promising but lead nowhere. Enumeration was critical to identify the actual entry points.
- Reporting Matters: Just like in my professional work, explaining the business impact and remediation was as important as the exploit itself.
- Mental Endurance: Unlike shorter exams, this is a marathon. Taking breaks to reset my perspective was vital when I got stuck on a specific WAF bypass.
Key Takeaways
- Automation has limits: This exam proved that while scanners are useful for reconnaissance, high-level exploitation requires a human brain to understand context and logic.
- Encoding is everything: Understanding how different databases and parsers handle encoded characters (URL, double URL, Hex, Unicode) is the difference between a blocked request and a shell.
- Patience with Blind SQLi: Extracting data blindly is tedious but necessary; mastering time-based payloads was essential.
Recommendations for Future Candidates
- Master Burp Suite: You need to be comfortable with Repeater, Intruder, and Decoder. Extensions like ‘Logger++’ can be very helpful.
- Don’t Overthink: sometimes the solution is complex, but often it’s about finding the one character that breaks the logic.
- Practice Local Labs: Set up local Docker containers with specific vulnerabilities (like old versions of Tomcat or vulnerable PHP apps) to practice deserialization in a controlled environment.
- Read the Letter of Engagement: Ensure you are attacking the scope correctly and meeting the specific requirements for the report deliverables.
I am proud to add the eWPTX credential to my professional portfolio. It has significantly improved my ability to assess complex web applications and deliver higher value during black-box penetration tests.
If you have any questions about the exam or want to discuss advanced WAF bypass techniques, feel free to reach out!
⭐️ Always learning, hacking, and building secure systems.